Blesta 3.0: Automation
Part of my job in the development of v3 is to take a step back and consider how each and every feature in Blesta can be improved over previous versions. Lots of thought, and many discussions surround even the simplest details of both the external and internal workings of Blesta, the visible and invisible.
Today I want to compare and contrast, and reveal how we handle automation in v3.
v2
Version 2 has a Cron Status & Setup page, under Settings > API/Cron Settings. The intent of this page is to show you when the cron last ran, how to set up your cron, and provide a method by which to run the cron manually. We were the first to secure the cron with a key, preventing it from being run by unauthorized users. Overall very basic, and it works pretty well.
v3
Version 3 does everything mentioned above, but in a simpler, more intuitive way — with the addition of being able to update the cron key right here. This key is now separate from the API key, which it shared in v2.

This is a good replacement for v2, and we could have stopped there.. but like I said in the opening, a lot of thought, many discussions.. and I’ll add, a lot of planning and development time goes into each and every feature.
One thing that bothers me a lot with v2 is that I can’t set exactly when I want a particular task to execute. Some tasks run once daily, some run every x minutes. The daily tasks run every day at midnight, and for the most part, the more frequent ones are at the mercy of how often the cron is scheduled to run.
This creates some issues, first of all is that midnight emails probably don’t have the highest read rate. Secondly, midnight account suspensions for non-payment result in emergency tickets at a time when most of your staff is sleeping or in the shower.
So, the actual cron job should run every 5 minutes, and you should be able to schedule when each task runs. Right? We think so. It’s almost common sense, but nobody has done it until now.

…
Above is what Invoice Creation and Auto Debit tasks look like. In this case, we have them both set up to run at 2pm daily. These are 2 tasks out of more than a dozen.
What about more frequent tasks?

This option illustrates how paid pending services, such as exist when a new order is placed, are provisioned.. every 5 minutes.
In addition to being able to schedule each task, they can also be explicitly disabled.
Developer Candy: Plugins can register automation tasks.
Another important thing to note is that all the times are in your local timezone — or whatever you set your timezone to be, regardless of the server time. Additionally, all dates and times in Blesta everywhere are stored in the database as and converted from UTC, which means you can change your timezone without affecting the stored value.
The default options will be perfect for most people, and there will be no real necessity to dig in and tweak these around.. Really, it’s not that important, but I wanted to show you for two reasons. 1. It’s a neat, practical feature and more importantly.. 2. It gives you a glimpse into how we work, how detail oriented we are, and how serious we are when it comes to usability.
Hope you have a nice weekend. Speaking of weekends…
Nerd Alert: If you play a game called Minecraft, we’ve got a Minecraft server up and running at 74.80.216.146. Come join us, some of our friends, and some of their friends as we build random stuff. HostMaster = Me, Awesomisitist = Tyson, Codelphious = Cody.
Related Tags:
Blesta 3.0: Software Licensing
Software licensing offers software developers a means of ensuring their product is not installed without prior authorization (generally by purchasing the product). Some competing products offer licensing modules to facilitate the deployment of such software, but their designs are critically flawed in a number of ways. Today I’ll describe the software licensing scheme we use in Blesta 3.0, and why it works. But first, let’s take a look at the problem.
To ensure an installation is allowed to run it needs to established its authenticity. This is generally done by “calling home.” That is, by contacting the licensing server. Information returned from the licensing server varies, but generally contains data about how, when, and where the software can run.
The naive approach
It goes without saying that if the license data can be tampered with one can easily bypass the license check. To resolve this, others have devised a scheme whereby the data is hashed using a shared secret salt know by the licensing server and by the product. When the product receives the license data it creates a hash from the data using the shared secret salt and compares that hash with the one that accompanied the data. If the two hashes match the data is trusted, otherwise the data is rejected.
Some systems don’t even bother sending the original hash of the data and instead compute and store the hash upon arrival for future reference. These systems are even less secure.
There are a number of exploits with these systems:
- Because the same shared secret is used to generate the hash across all installations it may be possible to obtain the shared secret
- Because the hashing method generally used is insecure it may be possible to tamper with the data and still produce the same hash (i.e. a hash collision)
- Because the data passed across the line is unencrypted or poorly encrypted it may be intercepted and the licensing server may be tricked into returning data regarding a separate valid license, or the licensing server may itself be spoofed
Exploiting it
Some may argue the dangers of revealing how insecure systems can be compromised, just as a magician might jeer at the sight of someone exposing their trickery. Those that argue from that position fail to realize that security does not arise out of obfuscation. Shannon’s maxim teaches that one must always assume that an attacker understands exactly how a system operates.
- Determine where the software calls home to. This can be done by monitoring network traffic or guessing the license server domain.
- Spoof the licensing server by modifying the server’s DNS or hosts file to resolve to a “license server” you create.
- Capture the data sent to the licensing server to a log file.
- Capture the data returned from the licensing server. This can be done by manually passing the data from #3 to the licensing server. Note that if you do not have information to obtain a valid response from the license server, you may be able to obtain that information from another user with a valid license or from a public demo of the application.
- Return the license data you capture from the license server, or modify it to ensure it continues to function ad infinitum.
The solution
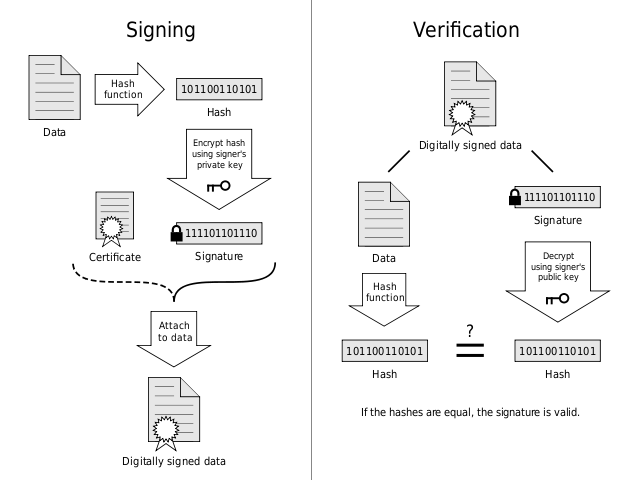
A digital signature allows us to verify the authenticity of a message through the use of an asymmetric key cipher, which uses one key (the private key) to encrypt data and an entirely different key (the public key) to decrypt data. Meaning that an attacker can not reproduce signature data since they do not have the private key.
How it works
- The license server generates a unique public/private key pair for the installation and delivers the public key securely to the installation
- The license server then encrypts the license data, generates a hash of the data and encrypts it using the private key to produce the signature
- The license server then delivers the data and signature to the installation
- The installation verifies the signature by decrypting the signature with the public key and comparing it with the hash it generates from the data
In the event that the signature can not be verified the license data is rejected and the license becomes invalid. Attempting to spoof the license server does nothing because only the license server can sign messages and the installation will only be able to verify signatures from the license server.
Additionally, at any time the license server may choose to generate a new key pair. This is especially useful because as attacks on asymmetric key ciphers becomes computationally cheaper it becomes increasingly important to cycle keys and/or increase key lengths.
Why are we telling you all this?
It would be great if there were no need for software license validation, but there is and there’s a market for it. Our philosophy is if you’re going to do something you ought to do it right. At the moment, thousands of developers put their software in the hands of licensing systems that provide illusory protection at best, and that’s unfortunate.
So, why are we telling you all this? Because we’re building a licensing plugin for v3 that does it right. We don’t mind sharing with everyone how it works because even licensing systems should be transparent. And, if our competitors decide to rework their licensing systems and do things right — then everyone is better off. And that’s what it’s all about.
Blesta 3.0: The database
A lot of effort has gone into designing and interfacing with the database in version 3, so I thought I’d share a little insight into some of the improvements we’ve made over version 2.
We’ve beefed up the database by making use of transactions, which allow us to add, edit, or remove items from the database with the ability to undo those changes should something go wrong. Because of this we’ve made the switch from a MyISAM storage engine to InnoDB (the default for MySQL as of version 5.5), making Blesta ACID-ic.
Another major improvement is the use of UTF8 collation, which will now allow users to more easily search the database in their native tongue as well as input and output data without conversion. This is a huge improvement for developers, and we are all about developers with version 3.
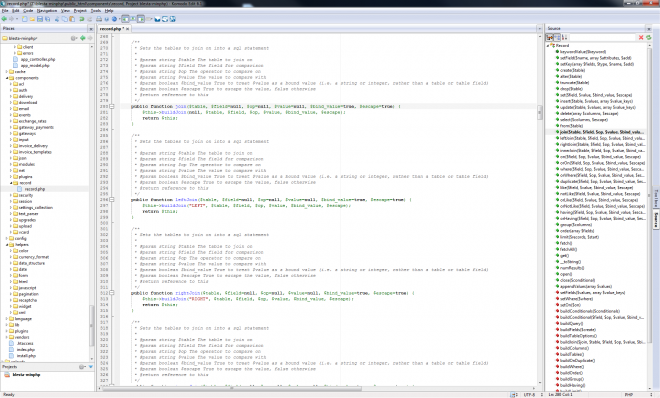
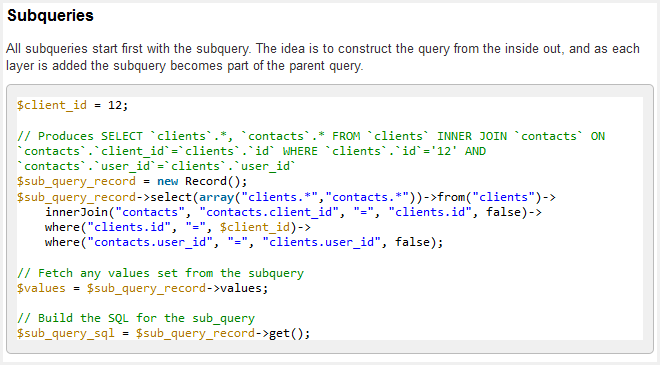
Speaking of developers, another great improvement is the introduction of the Record component. The record component is a database access object that creates queries using a series of method calls. Never again will you have to worry about which comes first, GROUP BY or ORDER BY.
In addition, the Record component uses the PDO library, making queries safe and secure. But that’s not the only benefit of PDO. Can we say “multi-database support”, as in MSSQL, PostgreSQL, and others? Well, no, not at the moment, but that’s definitely a possibility.
From the Developer Documentation:
Related Tags:
Blesta 3.0: Client Area
One thing we haven’t really talked about much is the client area. We have a good excuse: The vast majority of functionality is built into the staff/admin interface. But, the client experience is important too, arguably much more-so. In v2.x the client interface is identical in overall design to the admin interface with a slight color change.
In v3 we went a different direction. While there are similarities between the client interface and the admin interface they are completely different designs and you log into them independently.
Important notes to make about the client area in v3..
- The client interface has a new, clean & unique design.
- The client interface can be easily themed & integrated into an existing site.
- The client interface now consists of a Portal, Account Management, and Order System.
- The client interface is more intuitive and user friendly, and takes advantage of a lot of new features introduced in v3.
- Developers will be happy, Plugins can affect the client areas too.
- Mystery feature — yes I just did that, more details in a future post.
Portal, Account Management, and Order System. All tied together, all themed the same, all easily integrated into an existing site design.
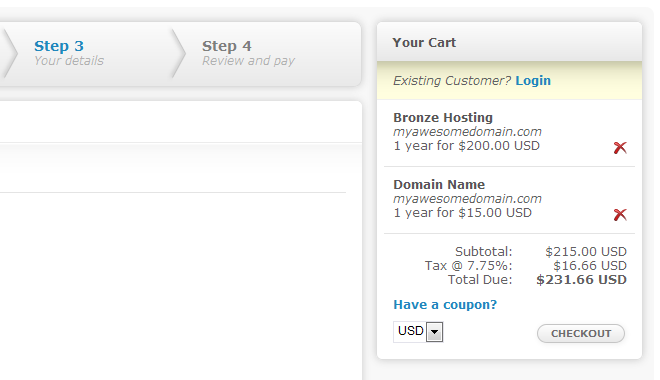
I can’t not leak some eye candy in a post, so above is a cropped segment of the default order template. I hope you agree, it’s a nice and clean design, yet fairly neutral in terms of color. Though the header is not shown here, it does have color and the color is easily changed.
There’s a lot more I could show you, but we’ll cover more in a future post. And to all a good weekend!